ACT Fibernet blocks sites using deep packet inspection
ISPs in India have been blocking websites since many years. It’s often done without much sense to it. The goveernment/telecom bodies and courts sometimes tell the ISPs to block content instead of telling the same to the websites that host the content. Sometimes, the orders are to block certain urls and ISPs are over-enthusiastic in implementing the orders and block complete websites. It’s all frustrating but it becomes enraging when you find out that the ISPs are messing with your traffic in a less than ethical way to implement this. Earlier, I pointed out how ACT was hijacking my DNS to implement the blocks. Now, they seem to have started doing something else, not sure if it is worse or better though. They are now doing deep packet inspection to find out the sites that I am visiting and thus block them by stopping the responses to my requests.
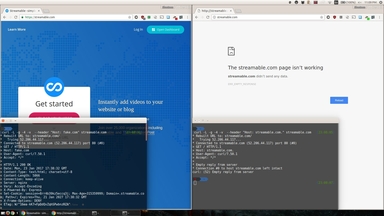
A few days ago, there were a few tweets mentioning that Streamable was blocked by few Indian ISPs. While checking it out, I noticed that I was not able to access it either on ACT ISP. I tried pinging the site and a traceroute to it and it seemed to work fine with no anomalies which puzzled me. Then I tried using https to access the site, and it opened up fine. This meant that ACT isn’t blocking the access based on the dns but by looking at something in my packets and so using https bypassed it (due to encryption of the data lying within).
I further tried doing the same through curl and found that if I fake the “Host” header in the command, I could access streamable.com even through http. A few other tests confirmed that ACT actually does a partial match for the blocked site because it blocked host headers like fakestreamable.com or streamable.com.in etc as well. But using something like “fake.com” worked. You can try this with below command and vary the site name after “Host:” in the command.
curl -L -g -4 -v --header "Host: streamable.com" streamable.com
I hope Indian ISPs can stop this malpractice of interfering with our data.