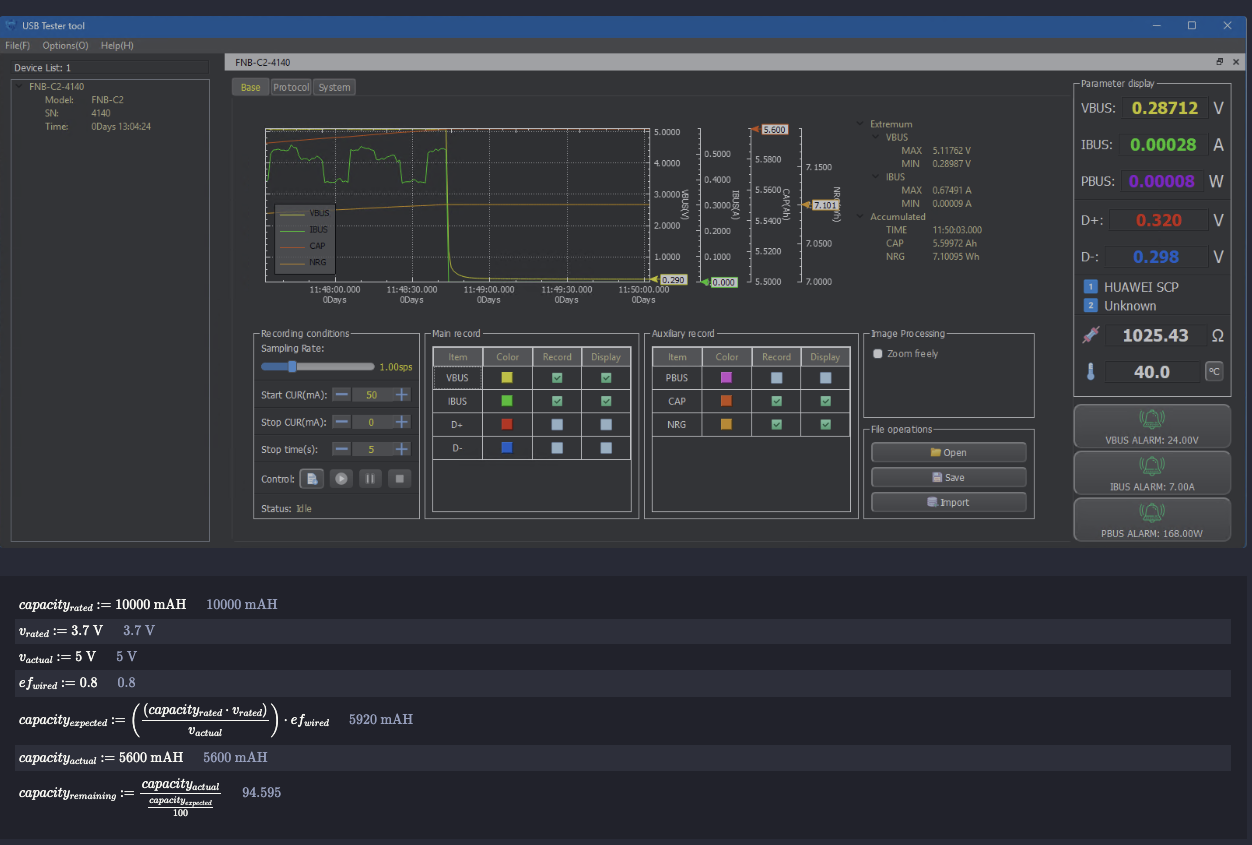
I Know Learnt Kung Fu
Imagine yourself in a Hollywood Thriller. You wake up in a dark room without any memory of how you got there or what are you doing there. All you know is you need to get out somehow but don’t have any instructions on how to do so. You can’t really see anything, but someone keeps shouting random words. Every time you do something, you either feel a sharp bout of pain or a bit of exhilaration that becomes your sole guide. Gradually, you figure out the connection between those random words and your actions and you start making your way through and soon see the light at the end of the tunnel.